External Red Team Assessment
Simulates real world attackers targeting internet facing assets to identify exploitable entry points, security gaps and weaknesses in perimeter defenses and monitoring controls.

Expert Red Teaming Services that simulate advanced cyber attacks to validate security controls and expose critical business risks.

Red Teaming is an advanced security assessment that simulates real world cyber attacks to evaluate how effectively your organization can detect, respond to, and withstand targeted threats.
Unlike traditional testing, Red Teaming Services focus on stealth, persistence and business impact. A comprehensive Red Team Assessment helps uncover hidden vulnerabilities, security blind spots and gaps in people, processes and technology.
Security tools alone cannot guarantee protection against determined attackers. Red Teaming Services simulate real world, targeted attacks to test how your people, processes, and technologies respond under pressure.
A comprehensive Red Team Assessment exposes hidden weaknesses, validates detection capabilities, and measures true incident response readiness before an actual breach occurs.
Our Red Teaming Services simulate advanced, real world attack scenarios to evaluate detection capabilities, response readiness and overall security resilience through structured Red Team Assessment engagements.
Simulates real world attackers targeting internet facing assets to identify exploitable entry points, security gaps and weaknesses in perimeter defenses and monitoring controls.
Assesses insider threat scenarios by testing lateral movement, privilege escalation and access to sensitive systems after initial compromise within corporate environments.
Evaluates human risk exposure through phishing, vishing, and impersonation campaigns to measure employee awareness and incident response effectiveness under realistic attack simulations.
Our Red Teaming Services help organizations validate real world security readiness, uncover hidden vulnerabilities, and strengthen cyber resilience through comprehensive, intelligence driven Red Team Assessment engagements.
Red Teaming Services simulate advanced adversaries to assess how effectively your security controls detect, prevent and respond to targeted cyberattacks.
A structured Red Team Assessment uncovers vulnerabilities traditional testing may miss, including weaknesses across people, processes and technology layers.
Red Teaming improves detection accuracy, response speed, and coordination by testing security teams under realistic, high pressure attack scenarios.
Our Red Teaming Services demonstrate how attacks could affect critical assets, operations, and sensitive data, enabling informed risk based decisions.
A comprehensive Red Team Assessment validates whether existing security tools and controls are configured and performing as intended.
Red Teaming provides leadership with clear insights into organizational resilience, helping align cybersecurity strategy with business objectives.
Our Red Teaming Services identify exploitable security gaps across systems, identities, processes and people through realistic, intelligence driven Red Team Assessment engagements.
A Red Team Assessment reveals exposed assets, weak perimeter controls, and misconfigurations that allow attackers to gain initial entry into your environment.
Our Red Teaming Services uncover excessive permissions, poor identity governance, and authentication weaknesses enabling unauthorized privilege escalation.
Red Team Assessment identifies segmentation failures that allow attackers to move between systems and access critical infrastructure.
Red Teaming Services expose gaps in logging, alerting, and response processes that delay or prevent threat detection.
A comprehensive Red Team Assessment identifies identity, storage and access control weaknesses in hybrid and cloud environments.
Red Teaming Services assess susceptibility to phishing and social engineering attacks that bypass technical controls.
Red Team Assessment uncovers insufficient controls preventing sensitive data extraction during simulated attack scenarios.
Our Red Teaming Services highlight delays in containment, communication gaps, and operational response challenges under pressure.
Actionable insights and evidence delivered through comprehensive Red Team Assessment engagements.
High level overview of Red Teaming findings, business impact and strategic risk exposure.
Comprehensive Red Team Assessment documentation covering attack paths, exploited vulnerabilities and supporting evidence.
Leadership level presentation explaining Red Team Assessment outcomes and resilience improvements.
Assessment of monitoring effectiveness, alert accuracy and incident response performance during engagement.
Screenshots, logs and proof demonstrating successful exploitation during Red Team Assessment.
Structured classification of identified weaknesses based on likelihood and business impact.
Clear, prioritized recommendations to strengthen defenses after Red Teaming engagement.
Step by step breakdown of Red Teaming activities mapped to real world attack techniques.
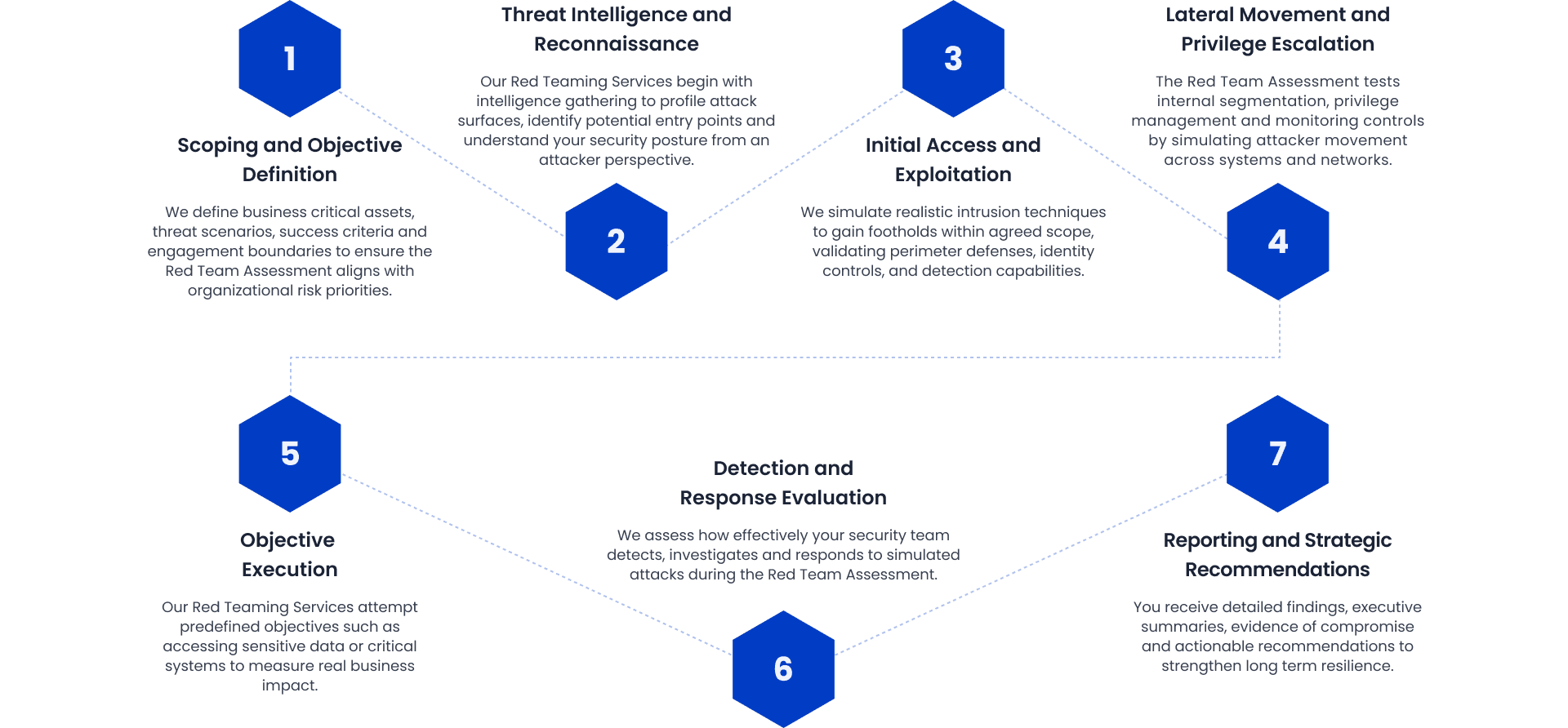
Our Red Teaming Services follow a strategic, intelligence driven approach to simulate real world adversaries and deliver measurable insights through a comprehensive Red Team Assessment.
Red Teaming Services validate real world attack resilience across critical industries.
Red Team Assessment protects financial systems, digital banking platforms and sensitive transaction data.
Red Teaming Services secure payment applications, APIs and cloud based financial ecosystems.
Red Team Assessment safeguards policyholder data, underwriting systems and claims processing platforms.
Red Teaming Services protect patient records, connected medical devices and clinical systems.

































Experience the firsthand testimonies of industry leaders on how our experts overcame their complicated technical challenges and optimized their sales funnel.
I recently had my company certified by CyberSigma Consulting Services, and it was a fantastic experience! Their team was professional, knowledgeable, and provided excellent guidance throughout the process. The customer support was responsive and friendly, making everything easy. I highly recommend CyberSigma Consulting Services for anyone looking for ISO certification.
Sr. ISMS Manager | FCI Pvt. Ltd.



Our Red Teaming Services deliver realistic, intelligence driven attack simulations that validate your true security posture. Through structured Red Team Assessment engagements, we help organizations measure resilience, reduce risk and strengthen long term cyber defense capabilities.
Our Red Teaming Services simulate advanced attacker tactics to test the effectiveness of real defenses.
We align every Red Team Assessment with critical assets and strategic business risks.
Our Red Teaming Services are led by seasoned professionals with proven offensive expertise.
Each Red Team Assessment delivers actionable insights that strengthen detection and response maturity.
Our Red Teaming Services provide structured reports for leadership and security teams.
From planning to remediation validation, our Red Team Assessment ensures continuous improvement.
We support organizations in strengthening cybersecurity posture, meeting regulatory obligations, and building lasting trust through specialized compliance consulting and comprehensive VAPT services.
Protect Android and iOS applications from data leakage, insecure storage, reverse engineering and authentication weaknesses.
Evaluate internal and external network infrastructure to identify misconfigurations, exposed services and exploitable vulnerabilities.
Assess API endpoints, access controls, authentication mechanisms and data validation processes to prevent unauthorized access and data breaches.
Our senior consultants will contact you to discuss a tailored strategy and provide a complimentary, no-obligation quote.


Locations we operate from
405, 4th Floor, Majestic Signia, Sector 62, Noida, Uttar Pradesh 201309
InCube Centre, Tejaswini Society, Lane 2, Aundh, PUNE, India, 411007
A802, Crescenzo, C /38-39, G-Block, Bandra Kurla Complex, Mumbai-400051, Maharashtra, India
Maharaj, 152/4, 8th Cross, Chamrajpet, Bengaluru, Karnataka, India, 560018
Business Point Building - Office No. 702 - Dubai - United Arab Emirates
L.L.C Muna AlJaziri Building, Office No 303 Al Mararr Dubai, UAE
19 Dr. Omar Dessouky Street, Cairo- Egypt 4271020
Level 4, 80 Market Street, South Melbourne 3205