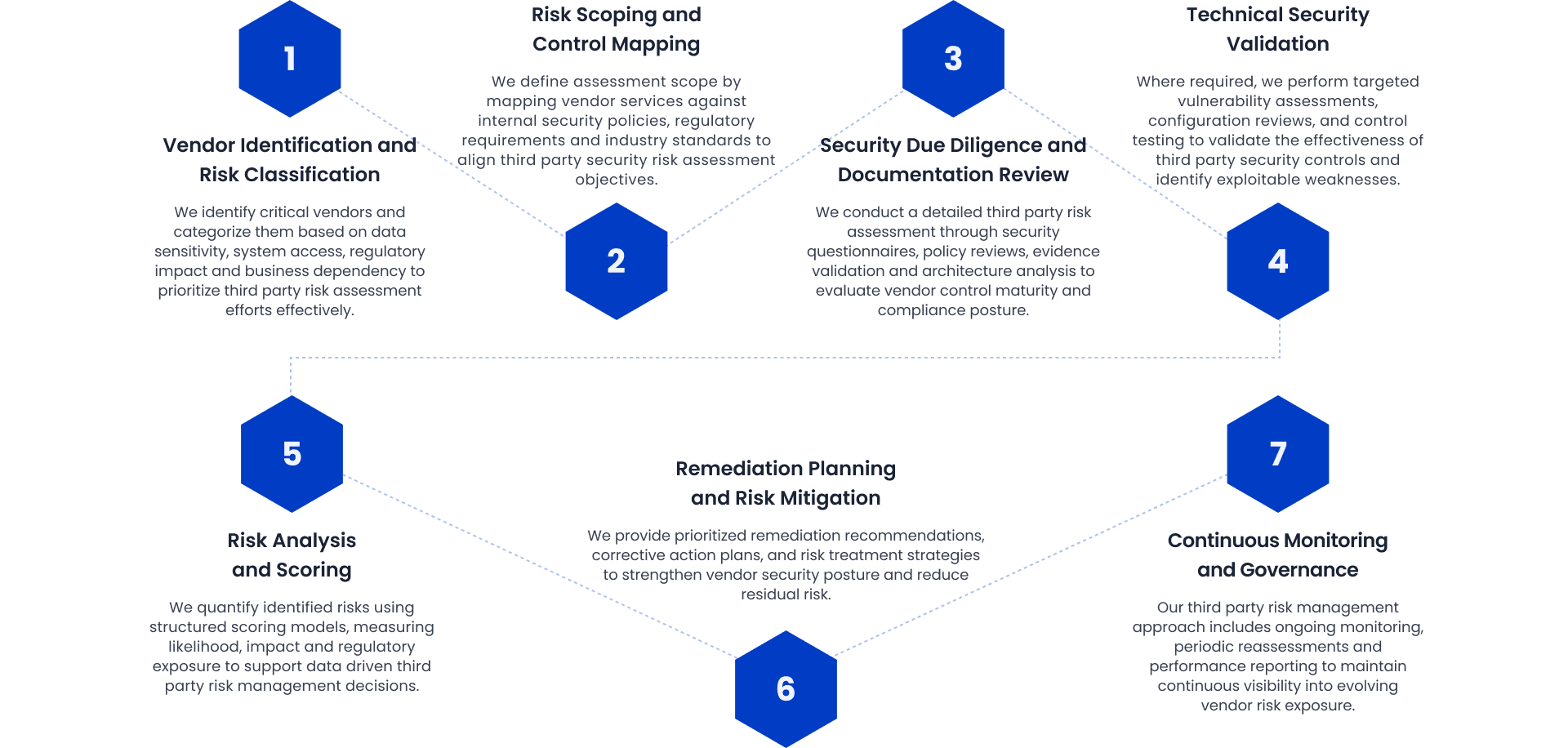
Vendor Security Risk Assessment
We perform a structured third party security risk assessment to evaluate vendor policies, technical safeguards, data handling practices, and infrastructure resilience, identifying control gaps and measurable cybersecurity risk exposure.




.png&w=384&q=75)
.png&w=384&q=75)
.jpg&w=384&q=75)
.png&w=384&q=75)
.png&w=384&q=75)
.jpg&w=384&q=75)
.png&w=384&q=75)
.jpg&w=384&q=75)